Packet-capture files have long been a forensic gold mine, yet most organizations still rely on manual Wireshark sessions, CLI dissectors, and signature-based IDS rules to extract value from them. Those workflows worked when networks were simple and a single PCAP rarely exceeded a few hundred megabytes. Microservices, zero-trust edges, and CI/CD pipelines that deploy dozens of times per day have made classic packet workflows a productivity bottleneck. Artificial intelligence changes the equation by automating deep-packet decoding, anomaly detection, and natural-language reporting — transforming static binary files into business-ready intelligence.
The Hidden Costs of Traditional PCAP Workflows
Most engineers learn early that packet captures do not lie. Unfortunately, extracting the truth demands a high human toll. Teams spend hours building nested display filters, paging through thousands of frames, and mentally reconstructing protocol state machines. Even seasoned experts can miss a subtle TCP window-shrink event or overlook a malicious TLS certificate chain when fatigue sets in at 3 AM. When capture size exceeds available RAM, analysts must slice files and lose global context. The business impact is clear — mean-time-to-resolution (MTTR) balloons, on-call stress increases, and revenue suffers during every minute of extended outage or security incident.
How AI Transforms Packet Analysis
AI eliminates repetitive decoding chores by leveraging models trained on millions of packet patterns. Instead of waiting for a human to spot an odd flag combination, an unsupervised anomaly model highlights flows that deviate from learned baselines and ranks them by statistical rarity. A natural-language generation layer then describes each finding in plain English — "This TLS handshake renegotiated from TLS 1.2 to TLS 1.0, increasing vulnerability to downgrade attacks" — and recommends mitigations. Because AI pipelines scale horizontally across cloud workers, terabyte-sized captures finish in minutes, enabling real-time triage during live incidents rather than retrospective autopsies days later.
What AI Means for Different Teams
End Users & Non-Specialists
Non-specialists often avoid packet tools because the learning curve is steep. An AI-powered SaaS removes this barrier by accepting a drag-and-drop upload and returning a polished PDF that narrates root causes and performance metrics in friendly prose. Marketing managers can forward the report to customers, customer-success teams can attach it to support tickets, and legal departments can archive it as audit evidence — all without opening a single .pcap in Wireshark.
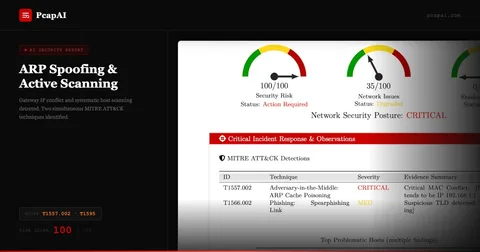
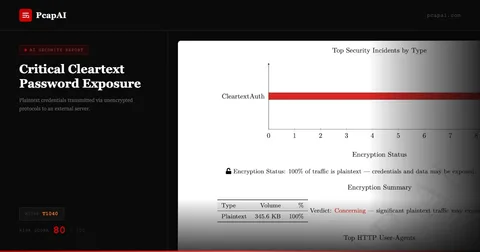
System Administrators & Security Engineers
Admins juggling firewall rules and vulnerability scans rarely have time to deep-dive every anomalous flow. AI surfaces credential leaks across SMB, POP3, or NTLM within seconds, flags lateral movement that follows a phishing foothold, and maps each behavior to the appropriate MITRE ATT&CK technique (T1040 for network sniffing, T1071 for application-layer C2, and so on). This condenses multi-hour hunts into a five-minute readout, freeing staff to respond to the highest-risk events rather than drowning in alert fatigue.
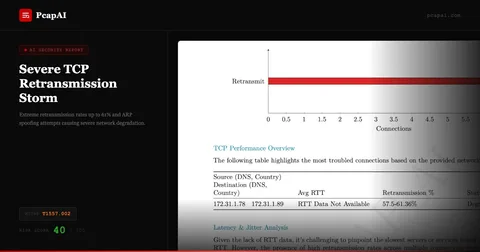
DevOps & SRE Teams
Continuous-delivery cultures treat performance regressions as release-blocking bugs. Integrating AI packet analysis into CI pipelines means every build produces a baseline network profile. If today's artifact introduces an extra handshake or unexpectedly truncates MSS options, the model increments a latency score and fails the pipeline before code hits production — keeping service-level objectives intact without relying on reactive, user-reported complaints.
Wireshark vs PcapAI: Side-by-Side
Manual (Wireshark)
Open file → build display filters → follow TCP streams → manually correlate flows → copy-paste into Word. Large captures take hours to document.
PcapAI
Upload file → AI ingests, parses, and maps findings to MITRE ATT&CK → executive PDF delivered in under 5 minutes.
From Proof of Concept to Production
Successful adoption begins with a pilot covering a single service path, such as user login. Upload historical captures representing normal traffic to establish baseline models. Next, integrate the SaaS API into staging to process nightly builds and validate stability. After two weeks of side-by-side comparison — AI alerts versus manual triage — graduate to production ingestion. Automate retention policies to purge captures after 60 minutes, satisfying GDPR's data-minimization mandate while preserving metadata summaries for long-term trending and SLA documentation.
ROI: Speed, Accuracy, and Cost
The chief advantage is speed: AI reduces MTTR by an order of magnitude and democratizes packet analysis, turning it from a specialist skill into a self-service diagnostic routine. The key risk is model accuracy — false positives can erode trust if unmanaged. Mitigate this by exposing confidence scores, permitting analyst overrides, and retraining models weekly on sanitized traffic representing new deployments. A consumption-based AI service scales with need: sandbox environments incur negligible expense while production spikes pay their own freight. Compare that to the hidden payroll cost of engineers lost in Wireshark for days and the ROI becomes clear.
Turning Packets into Competitive Advantage
AI-powered PCAP analysis is not merely a faster way to read packets — it is a strategic enabler. By converting raw network telemetry into narrative, role-specific insights, organizations gain sharper visibility, stronger security posture, and shorter delivery cycles. Instead of choosing between velocity and reliability, teams achieve both. Try AI-powered PCAP analysis or review our pricing tiers to get started.
Who Benefits Most from AI PCAP Analysis
The productivity gains from AI-powered PCAP analysis scale with volume and complexity. SOC teams handling dozens of captures per week gain the most: automated first-pass analysis compresses per-investigation time from hours to minutes, letting senior analysts focus on exception handling rather than routine triage. MSSPs and consulting firms gain a commercial advantage — faster reporting cycles allow them to absorb more clients without proportional headcount growth. Incident responders benefit during the most time-sensitive phase: an AI-generated brief identifying C2 beaconing (MITRE T1071), active exfiltration (T1048), and compromised hosts gives the responder an immediate prioritization framework before a single Wireshark filter is written.
Network engineers use AI PCAP analysis for performance troubleshooting: identifying the specific flows causing latency, quantifying retransmit rates, and isolating the application layer responsible. The common thread across all roles is the same — less time on mechanical data processing, more time on judgment and action.
AI PCAP Analysis vs. Traditional Scripted Workflows
Many security teams maintain custom Python scripts using libraries like scapy or pyshark to automate parts of PCAP analysis. These scripts are brittle: they break on unexpected protocol variants, require maintenance as attack techniques evolve, and produce raw data outputs rather than analyst-ready narrative. AI-powered platforms adapt to novel traffic patterns without script updates, cover 50+ detection techniques simultaneously, and produce structured reports that are ready to share with stakeholders. The scripts are not wrong — they are just solving a different problem. Use scripts for targeted, repeatable extraction tasks; use AI platforms for comprehensive forensic analysis and documentation.
Frequently Asked Questions
What are the main benefits of AI-powered PCAP analysis?
AI-powered PCAP analysis reduces mean-time-to-resolution by automating packet parsing, anomaly detection, and report generation. It maps findings to MITRE ATT&CK, surfaces credential leaks and C2 beaconing in seconds, and produces executive-ready PDFs without requiring Wireshark expertise.
How does AI PCAP analysis compare to manual Wireshark work?
Manual Wireshark analysis of a large capture typically takes hours of skilled analyst time. AI-powered analysis delivers the same coverage — including behavioral anomaly detection, GeoIP mapping, and TLS fingerprinting — in under five minutes, with consistent output every time.
Can AI detect zero-day threats in packet captures?
Yes. Unlike signature-based IDS tools that only flag known patterns, AI models use statistical anomaly detection and behavioral analysis. They recognize DGA domains, unusual beaconing intervals, and protocol skew even when no signature exists for the specific threat.
Is AI PCAP analysis suitable for DevOps and SRE pipelines?
Absolutely. AI packet analysis integrates into CI/CD pipelines to provide a network baseline per build. Regressions — unexpected handshakes, MSS changes, or latency spikes — are flagged automatically before code reaches production, keeping SLOs intact.