What's Actually in That PCAP?
Credentials, C2 beacons, DNS tunneling, lateral movement - PcapAI finds what matters and tells you exactly where to look. Upload once, get a full forensic report.
How it works
Drop your capture file
No setup, no agents to install
AI runs the investigation
Threats surface in under 1 minute
Get a board-ready report
Findings ranked, remediation included
TLS 1.3 · Isolated containers · Auto-purge in 24 hours
Key Features
You Have 47,000 Packets. We Have a Map.
You open the PCAP. 47,000 packets. Where do you even start? PcapAI maps every protocol layer, reconstructs flows and flags what matters — so you're not grep-ing through hex at 2am.
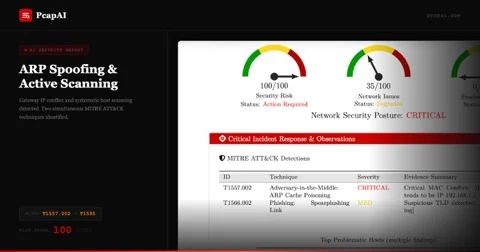
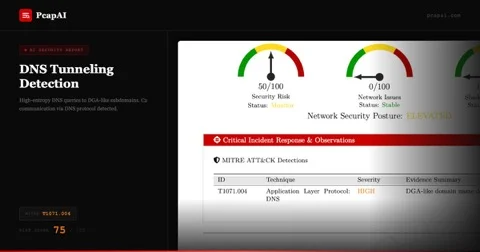
Attacks Are Designed to Look Normal
DNS tunneling doesn't look like an attack. Neither does a slow C2 beacon. That's the point. Our models were trained specifically on traffic that's designed not to stand out.
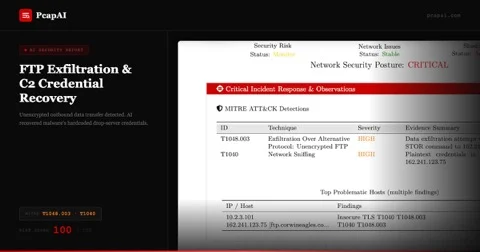
The Breach Happened. Now What?
Post-breach, every minute counts. Drop your PCAP in and get a list of exposed credentials, NTLM hashes and Kerberos tickets across SMB, HTTP and FTP — before your attacker moves laterally.
Users Are Complaining. Here's Why.
Users are complaining. You have a PCAP and a deadline. Retransmissions, latency spikes, congestion windows — PcapAI pulls it into one dashboard and tells you where to look first.
Built for Pipelines, Not Dashboards
REST or CLI. Auto-upload from CI, push findings to your SIEM, build your own alerting on top. Full docs, no vendor lock-in, works with whatever stack you already run.
A Report Your Team Can Actually Act On
The report doesn't just tell you what's wrong — it tells you what to do next. Findings ranked by severity, mapped to MITRE ATT&CK, with remediation steps your team can actually act on today.
View full ATT&CK coverageNot Sure It's Worth It?
Upload any PCAP for free. If PcapAI doesn't find anything interesting - fair enough. If it does, you'll know in two minutes.