The PCAP (Packet Capture) file is network forensics' ground truth — every bit, every header, every handshake is in there. For most SOC analysts, it is also a source of significant frustration. Parsing raw traffic is a grueling manual process, and as network speeds increase and encrypted traffic grows, the sheer volume in a typical capture creates analysis paralysis. Security teams spend hours in Wireshark filtering thousands of packets just to answer one question: Is this traffic malicious?
AI-driven automation changes this. By moving from PCAP to PDF through automated parsing and LLM-based analysis, teams transform raw binary data into professional, executive-ready reports in seconds. This post walks through exactly how that pipeline works.
Why Manual PCAP Analysis Fails to Scale
The traditional workflow is fundamentally broken. Analysts follow a repetitive cycle: open a massive file, apply dozens of display filters, manually correlate flows, export screenshots, and write summaries. This is not only slow — it is prone to human error. In a high-pressure SOC environment, time spent staring at hex is time away from actual threat hunting. The gap between a technical finding and a report a CISO can understand is often too wide, causing delayed remediation.
Manual triage of a large PCAP in Wireshark takes hours. Filtering out benign traffic, correlating suspicious flows, and writing the incident summary adds another hour on top — time that does not scale when a SOC team handles dozens of captures per week.
Phase 1: Intelligent Parsing and Metadata Extraction
The first step is efficient parsing. Automated systems deconstruct packets using high-speed parsers that extract structured metadata at scale — no tshark one-liners required. Key features extracted include:
- Flow statistics: duration, byte counts, packet intervals, and direction ratios.
- Protocol hierarchy: layer identification from Ethernet to application data, including TLS SNI and HTTP User-Agents.
- Credential exposure: automatic identification of plaintext credentials in cleartext traffic (T1040 — Network Sniffing).
By converting binary noise into structured JSON, we prepare the ground for higher-level AI reasoning.
Phase 2: AI Pattern Recognition and Anomaly Detection
Once data is structured, Large Language Models take over. Unlike signature-based IDS, AI-driven analysis understands context. The AI analyzes extracted flows to identify:
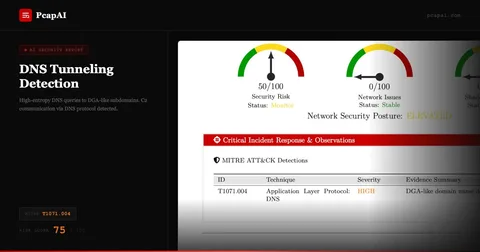
- Anomalous behavior: unusual beaconing intervals or non-standard ports used for common protocols (T1071 — Application Layer Protocol).
- Attack sequences: recognizing the stages of a cyberattack, from initial scanning through to data exfiltration (T1048).
- Contextual correlation: connecting failed logins to a sudden burst of outgoing encrypted traffic.
Phase 3: Actionable Recommendations, Not Just Findings
A report is useless without a next step. The true power of AI in network forensics is generating specific remediation actions from each finding. If the AI detects a potential SQL injection attempt, it provides concrete steps — check WAF logs for status-200 responses on the flagged URIs, review the source IP, validate input sanitization on the affected parameter. This moves the SOC from a reactive "detect" phase to a proactive "remediate" phase immediately.
Wireshark vs PcapAI: The Speed Gap
Manual (Wireshark)
Open file → apply display filters → follow TCP streams → correlate flows → write summary → format PDF. Total: 3–5 hours per investigation.
PcapAI
Upload PCAP → AI parses, correlates, and generates MITRE-mapped executive PDF. Total: under 5 minutes.
Bridging Technical Findings and Executive Communication
Technical findings must reach stakeholders who don't speak Wireshark. A core benefit of SOC automation is generating a professional PDF that serves two audiences simultaneously: analysts get detailed flow tables and packet-level evidence, while executives receive a high-level summary, risk score, and a clear impact statement. Standardized, automated PDFs make documentation consistent across every incident — invaluable for compliance, audits, and long-term trend analysis.
The Five Stages of the AI PCAP-to-Report Pipeline
Understanding what happens between "upload" and "PDF download" helps security teams evaluate AI PCAP tools accurately and integrate them into existing workflows. PcapAI processes every capture through five sequential stages, each building on the last.
Stage 1 — Ingestion and metadata extraction: The platform parses packet headers across all layers — Ethernet, IP, TCP/UDP, and application. It extracts flow tuples (source IP, destination IP, port, protocol, timestamp), calculates per-flow byte volumes and packet counts, and identifies protocols through deep packet inspection rather than relying solely on port numbers. A file transfer disguised over port 443 is identified by payload characteristics, not port assignment.
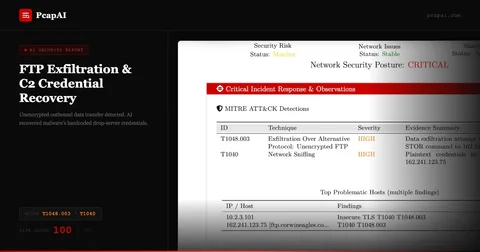
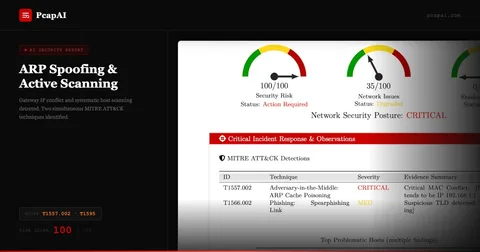
Stage 2 — Behavioral analysis: The engine runs 50+ MITRE ATT&CK-aligned detectors in parallel. Beaconing detection (T1071) measures inter-packet timing regularity. Exfiltration detection (T1048) flags high-volume outbound flows to unusual destinations. Credential harvesting detection (T1040) identifies cleartext authentication attempts across HTTP, FTP, SMTP, and Telnet. Each detector fires independently and contributes a weighted finding to the overall risk score.
Stage 3 — Enrichment: Detected IPs and domains are enriched with GeoIP data, ASN ownership, and threat intelligence signals. A destination belonging to a residential ISP in an unexpected country carries different weight than one belonging to a known CDN.
Stage 4 — Narrative generation: A large language model receives the structured findings and produces analyst-ready prose: what happened, in what sequence, with what probable intent. MITRE T-codes are explained on first use. Technical evidence is bolded for scannability. The output is calibrated for a SOC analyst — specific enough to guide investigation, concise enough to read in two minutes.
Stage 5 — PDF assembly: The executive summary, visual triage charts, AI narrative, and technical appendix are composed into a structured PDF. The document is layered: a CISO reads pages 1–2; an engineer reads the full report. Both audiences get the depth they need without wading through irrelevant detail.
What "Actionable" Actually Means in a PCAP Report
An actionable finding is one that a specific person can act on in a specific way. "Suspicious traffic detected" is not actionable. "Host 192.168.1.45 is communicating with AS14061 (DigitalOcean) at 60-second intervals consistent with C2 beaconing (T1071) — isolate the host and revoke its network access pending forensic review" is actionable. Every finding in a PcapAI report follows this formula: evidence → MITRE classification → recommended next step. The result is a document that drives incident closure, not just incident awareness.
Frequently Asked Questions
How does AI convert a PCAP file into a PDF report?
AI PCAP analysis works in three phases: (1) high-speed ingestion and metadata extraction, (2) behavioral anomaly detection and MITRE ATT&CK mapping using LLMs, and (3) natural language generation that assembles findings, risk scores, and remediation steps into a structured PDF — all in under five minutes.
What is automated network traffic analysis?
Automated network traffic analysis uses AI models to parse PCAP files, extract flow metadata, detect behavioral anomalies, and generate human-readable reports — replacing the manual Wireshark-based investigation workflow. It covers credential exposure (T1040), C2 beaconing (T1071), and data exfiltration (T1048) without requiring analyst expertise.
How does AI reduce MTTR in SOC workflows?
By automating the most time-consuming parts of incident response — parsing, correlation, and report writing — AI cuts mean-time-to-respond from hours to minutes. Analysts receive a pre-analyzed report with specific remediation steps, skipping the research phase and moving directly to containment.
Stop Wasting Hours on Manual Reporting
Upload your first PCAP and get actionable, MITRE ATT&CK-mapped insights in under five minutes.