PcapAI MCP Server Integration
Transform your AI assistant into an autonomous SOC analyst. The PcapAI MCP (Model Context Protocol) server allows AI agents like Claude Desktop to perform deep packet inspection and network forensics directly from your local machine, securely analyzing large .pcap and .pcapng files without sending raw packet data to the cloud.
What You Can Do
Once connected, Claude Desktop gains direct access to PcapAI's forensics engine. You can ask natural-language questions about any local PCAP file and receive structured, actionable findings:
Threat Detection
Identify C2 beaconing, malware exfiltration, port scanning, and credential exposure across TCP/UDP flows.
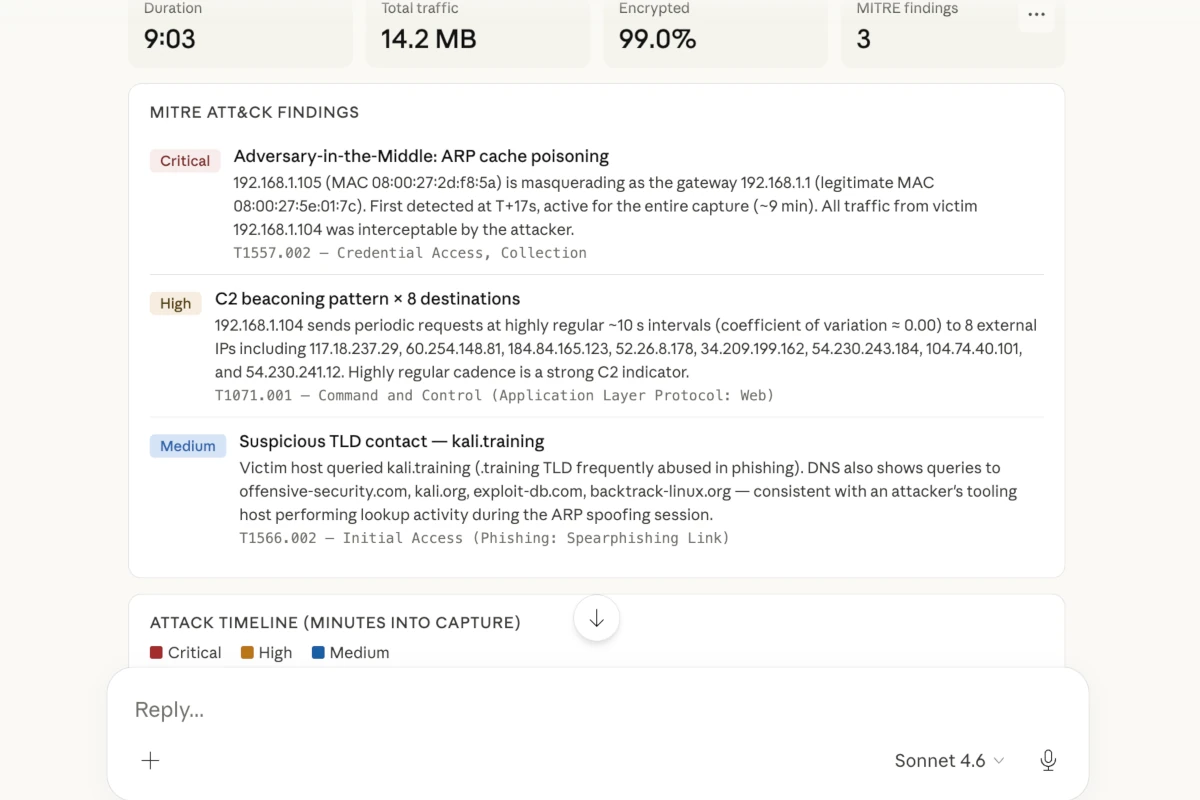
MITRE ATT&CK Mapping
Automatically correlate observed network behaviour to ATT&CK techniques and sub-techniques.
Protocol Analysis
Deep inspection of DNS, TLS, HTTP, FTP, and SMTP traffic with anomaly flagging and certificate validation.
Automated Reports
Generate structured PDF incident reports from forensic findings — ready for ticketing systems or post-incident review.
Open Source Repository
The MCP server is 100% open-source and written in Rust. Pre-built binaries for all supported platforms are available on GitHub Releases — no Rust toolchain required unless you want to build from source.
Installation
The server ships as a single self-contained binary. Choose the method that suits your environment.
Option A — Download Pre-built Binary (recommended)
Head to the GitHub Releases page and download the archive for your platform:
| Platform | File |
|---|---|
| macOS (Apple Silicon) | pcap-ai-mcp-macos-arm64 |
| macOS (Intel) | pcap-ai-mcp-macos-amd64 |
| Linux (x86_64) | pcap-ai-mcp-linux-amd64 |
| Linux (ARM64) | pcap-ai-mcp-linux-arm64 |
| Windows (x86_64) | pcap-ai-mcp-windows-amd64.exe |
Extract the archive and place the pcapai-mcp binary somewhere on your PATH, for example /usr/local/bin on macOS/Linux.
Option B — Build from Source with Cargo
If you have the Rust toolchain installed, you can build the latest version directly:
git clone https://github.com/pcap-ai/mcp-server.git
cd mcp-server
cargo build --releaseConfiguration
After installation, register the server with Claude Desktop by editing its configuration file.
Step 1 — Edit claude_desktop_config.json
The file is located at:
- macOS:
~/Library/Application Support/Claude/claude_desktop_config.json - Linux:
~/.config/Claude/claude_desktop_config.json - Windows:
%APPDATA%\Claude\claude_desktop_config.json
Add the following entry under mcpServers:
{
"mcpServers": {
"pcapai": {
"command": "/usr/local/bin/pcapai-mcp",
"env": {
"PCAPAI_API_KEY": "your_api_key_here"
}
}
}
}Step 2 — API Key (optional for guest mode)
The server works out of the box in guest mode without an API key — core analysis features are available immediately. To unlock Premium capabilities (larger file support, higher rate limits, advanced threat hunting), set your PCAPAI_API_KEY in the config above or as a shell environment variable:
export PCAPAI_API_KEY="your_api_key_here"
You can generate an API key from your account settings.
Step 3 — Restart Claude Desktop
Fully quit and relaunch Claude Desktop. The PcapAI tools will appear in Claude's tool palette. You can verify the connection by asking: "What PcapAI tools do you have available?"
Example Prompts
Once connected, you can ask Claude forensic questions about any local PCAP file by providing its path:
"Analyze /captures/incident.pcap and summarize all suspicious outbound connections."
"Does this capture contain any DNS beaconing or tunnelling activity?"
"Map the traffic in this PCAP to MITRE ATT&CK techniques and generate a PDF report."
"Extract all cleartext credentials visible in this packet capture."
"Which hosts are communicating on non-standard ports and what protocols do they resemble?"
API Connection Details
Under the hood, the MCP server communicates with the PcapAI core engine via our dedicated API endpoint. All packet parsing happens locally — only distilled forensic metadata is transmitted.
Note: Set PCAPAI_API_KEY in your environment or config to enable Premium features. Without a key, the server runs in guest mode with core functionality available at no cost.
