The Challenge: Spotting Stealthy DNS Data Exfiltration
DNS is the most trusted protocol on any enterprise network — and advanced threat actors know it. Because almost all corporate firewalls explicitly allow outbound UDP traffic on port 53, attackers routinely hide command-and-control (C2) channels and exfiltration payloads inside legitimate-looking DNS queries.
The result: security teams hunting for Data Exfiltration over alternative protocols are buried under millions of legitimate queries from web browsing, cloud telemetry, and antivirus updates. The malicious traffic blends in perfectly — and manual analysis can take days.
Applying basic Wireshark display filters like dns.qry.name.len > 50 or dns.qry.type == 16 (TXT records) yields thousands of false positives daily from legitimate CDNs and endpoint tracking domains.
Detecting Domain Generation Algorithms (DGA) mathematically requires exporting PCAP files to CSV and running custom Python entropy scripts across hundreds of thousands of queried domains — before you've even found the threat.
"We filtered our network traffic for anomalous TXT records, but the Cobalt Strike beacon was hiding in plain sight using dynamically generated A-records with low TTL values. Manually correlating the malicious DNS requests to the infected endpoint took our SOC analysts three days of tedious protocol analysis."
— SOC Lead, Enterprise Technology Company
The Solution: AI-Powered DNS Payload Analysis
PcapAI automates the mathematical heavy lifting required for modern DNS forensics. Instead of writing entropy scripts or battling alert fatigue, our deep packet inspection engine instantly analyzes the lexical structure, query frequency, and payload entropy of every DNS packet in your capture. The result: malicious exfiltration separated from background noise in seconds, not days.
-
✦
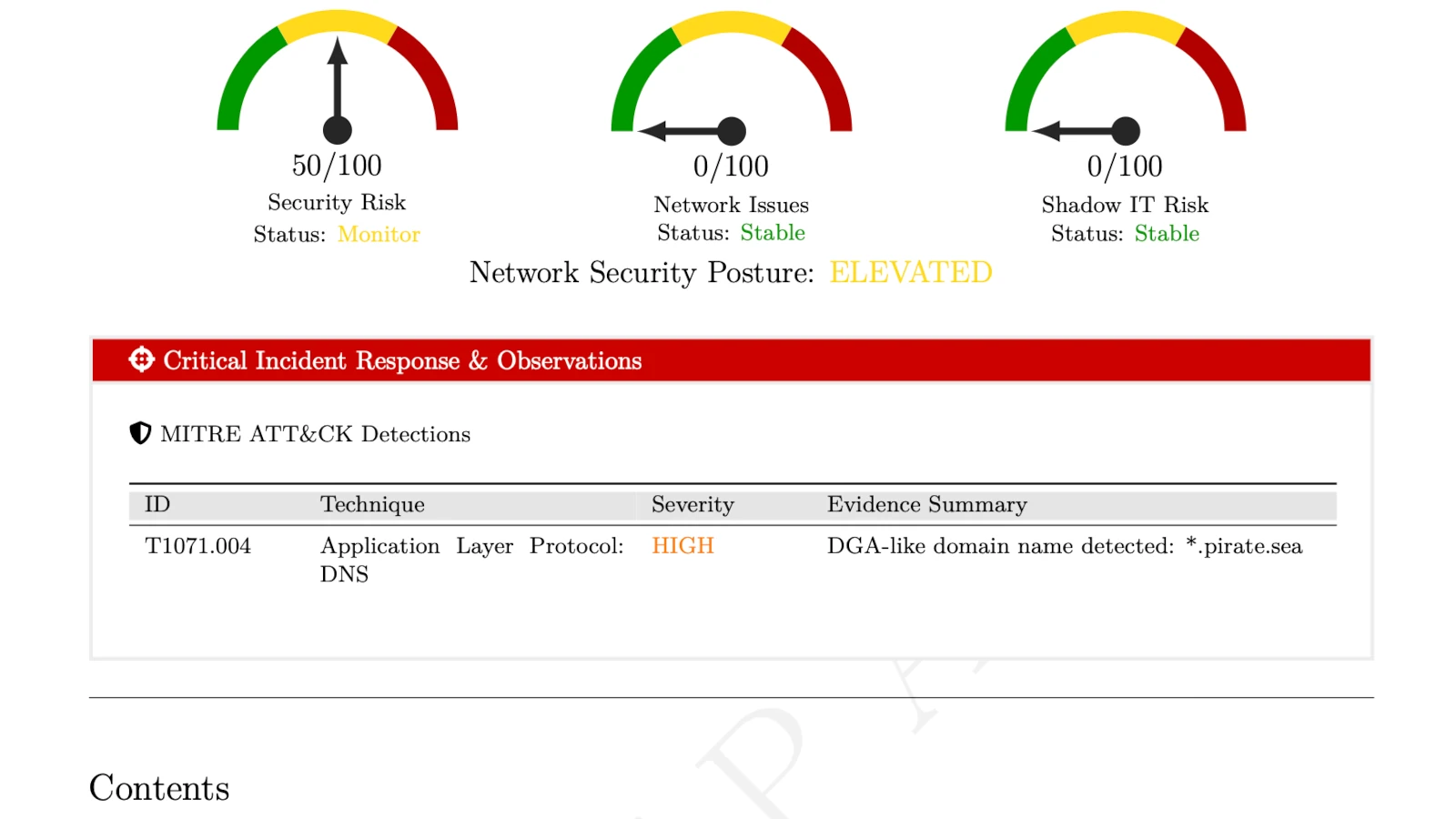
MITRE T1071.004 (Application Layer Protocol: DNS): instantly identifies large Base64-encoded subdomains (e.g.,
dGVzdGRhdGE.malicious.com) being used to silently exfiltrate stolen credentials outside the corporate perimeter. -
✦
MITRE T1568.002 (Domain Generation Algorithms): flags algorithmically generated domains (e.g.,
x8f9q2p.malicious.com) exhibiting high Shannon entropy — detecting malware variants that routinely bypass static threat intelligence blocklists. - ✦ Automated Noise Reduction: smart baselining filters out legitimate high-volume background noise from CDNs and cloud telemetry, eliminating the false positives that make manual analysis so time-consuming.
-
✦
Root Cause Correlation: automatically links anomalous DNS tunneling activity back to the infected internal host IP (e.g.,
192.168.1.105), giving incident responders the exact target for immediate quarantine.
Wireshark Manual Analysis vs. PcapAI
Manual (Wireshark) — 2.5GB PCAP
Exporting DNS logs to CSV, running custom Python entropy scripts, and manually sorting through CDN false positives. Process takes 1–3 hours.
PcapAI — 2.5GB PCAP
Instant lexical analysis, DGA entropy scoring, and automated MITRE framework mapping. Process takes under 20 seconds.
How It Works
Upload Your PCAP
Drop any .pcap or .pcapng file. No installation, no account required. Works with captures from any network device.
AI Analyzes Every DNS Packet
Our engine scores query entropy, detects DGA patterns, and baselines legitimate CDN traffic — across every single DNS record in your capture.
Get the Infected Host
Receive a full report with the C2 domain, infected endpoint IP, MITRE ATT&CK mappings, and containment steps — ready to act on immediately.
Frequently Asked Questions
How do you detect DNS tunneling in Wireshark?
To manually detect DNS tunneling in Wireshark, analysts typically filter for long queries using dns.qry.name.len > 50 or unusual TXT records with dns.qry.type == 16. This produces massive false positives from legitimate CDNs and requires custom Python entropy scripts to identify DGA domains — a process that can take 1–3 hours on a large capture. PcapAI automates the full entropy analysis and separates malicious payloads from background noise in seconds.
What is MITRE ATT&CK T1071.004?
MITRE ATT&CK T1071.004 describes adversaries using DNS as an Application Layer Protocol to communicate with C2 servers or exfiltrate sensitive data. Attackers favor this technique because port 53 is rarely blocked by corporate firewalls, making DNS an ideal covert channel for both data theft and persistent malware beaconing.
What is a Domain Generation Algorithm (DGA)?
A Domain Generation Algorithm is a technique used by malware to automatically produce large numbers of pseudo-random domain names that act as potential C2 rendezvous points. Instead of hardcoding a C2 server address — which can be easily blocklisted — the malware generates hundreds of domains daily, with only the attacker knowing which ones are active. DGA domains typically exhibit high Shannon entropy and unusual character distributions that distinguish them from legitimate domain names.
Can DNS tunneling bypass a firewall?
Yes — and that is exactly why attackers use it. Most corporate firewalls allow outbound DNS traffic on UDP port 53 without inspection. By encoding data inside DNS query subdomains or TXT record responses, an attacker can exfiltrate gigabytes of data or maintain a persistent C2 channel through firewalls that would block any other outbound connection. Deep packet inspection at the DNS payload level — as PcapAI performs — is required to detect it.
What tools detect DNS tunneling automatically?
Live network monitoring tools like Zeek and Suricata can alert on DNS anomalies in real time, but require significant tuning to reduce false positives. For post-incident forensics from a PCAP file, PcapAI automates the full analysis — entropy scoring, DGA detection, MITRE ATT&CK mapping, and infected host identification — in under 60 seconds without any manual filtering or scripting.
Related Use Cases
Is there a C2 beacon in your traffic?
Upload any PCAP from your network and find out in under 60 seconds. No installation, nothing stored after 24 hours. Or view pricing for enterprise API access.
AI Analysis Output (Sample)