The Challenge: Hunting Layer 2 Threats in the Noise
Detecting an Adversary-in-the-Middle (AitM) attack — such as ARP Cache Poisoning — within a large network capture is like finding a needle in a haystack. Address Resolution Protocol (ARP) traffic is inherently noisy, constantly broadcasting legitimate queries across the local subnet to map IP addresses to physical MAC addresses.
Standard firewalls operate at Layer 3 and above, making them completely blind to these Layer 2 deception tactics. When a malicious insider or compromised endpoint begins broadcasting forged ARP replies to intercept internal traffic, incident responders are forced into a highly manual analysis workflow — drastically increasing mean-time-to-respond (MTTR) while the adversary silently exfiltrates data.
Relying on Wireshark filters like arp.duplicate-address-detected often yields false positives from misconfigured DHCP servers, requiring engineers to manually correlate MAC conflicts with the legitimate subnet gateway (e.g., 192.168.1.1) over hours of analysis.
Before an attacker executes an ARP spoofing attack, they perform Active Scanning (MITRE T1595) to map the subnet. Identifying these stealthy Nmap or ARP sweeps requires correlating thousands of fragmented TCP and UDP packets by hand.
"By the time our SOC team downloaded the 5GB PCAPNG file from the core switch and manually filtered the ARP streams to prove host 10.0.5.22 was impersonating the default gateway, the attacker had already intercepted the unencrypted FTP credentials and moved laterally into our database tier."
— Senior Network Engineer, Financial Services
The Solution: AI-Driven Automated Forensics
PcapAI completely eliminates manual packet hunting by applying advanced deep packet inspection and heuristic modeling directly to your raw traffic data. Instead of relying on static, single-packet Wireshark filters, our engine continuously tracks the global ARP state machine across the entire capture. Within seconds, it reconstructs the local network topology, surfaces behavioral anomalies, and provides incident responders with definitive proof of Adversary-in-the-Middle interception.
-
✦
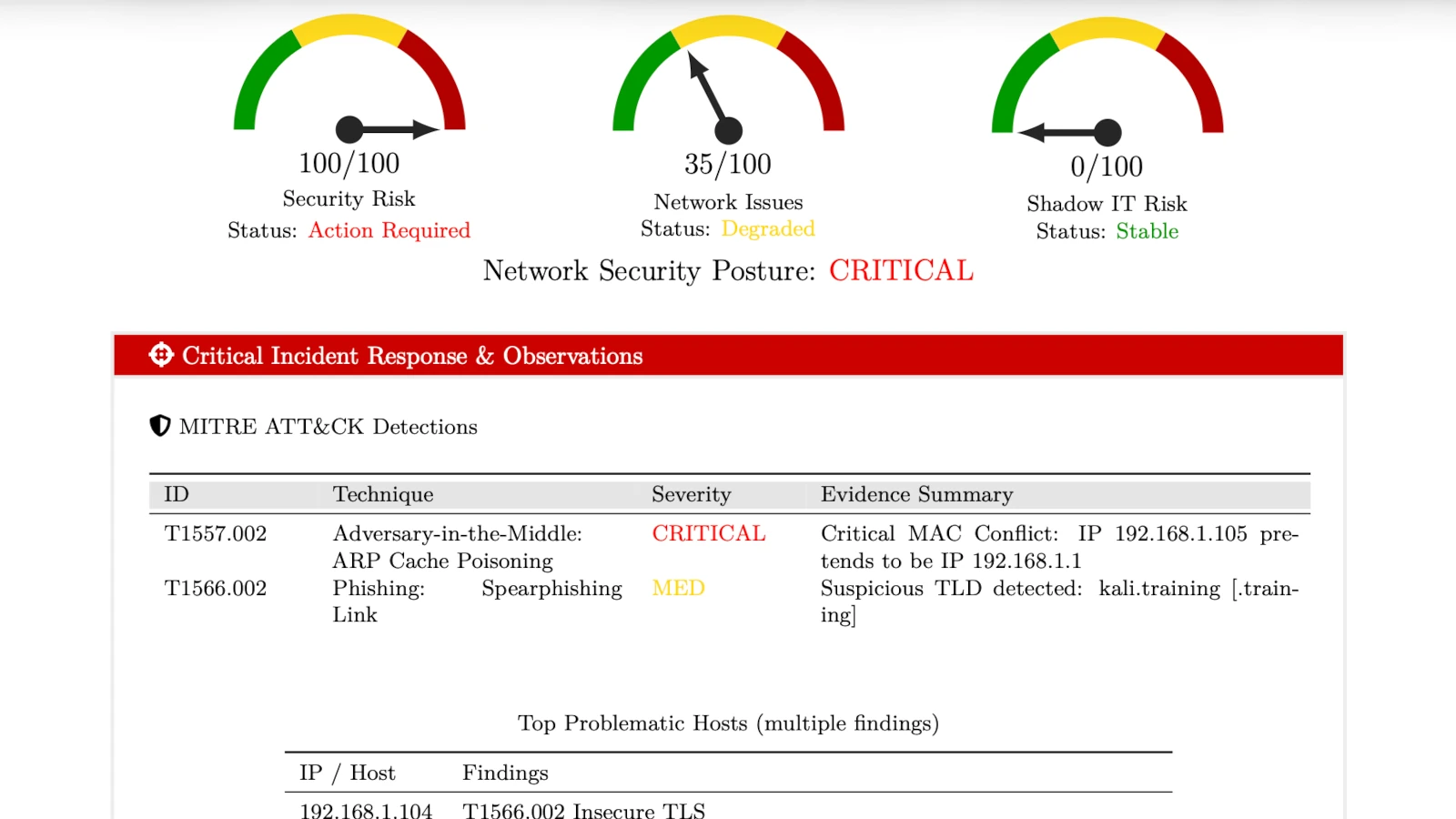
MITRE T1557.002 (ARP Cache Poisoning): definitively identified host
192.168.1.105maliciously broadcasting unsolicited ARP replies to claim the MAC address (00:1A:2B:3C:4D:5E) of the legitimate subnet gateway, intercepting outbound traffic. -
✦
MITRE T1595.001 (Active Scanning): automatically flagged rogue endpoint
192.168.1.105for executing aggressive TCP SYN scans across the local/24segment immediately prior to the poisoning attack. - ✦ MITRE T1040 (Network Sniffing): correlated the ARP spoofing event with secondary cleartext credential exposure, proving the attacker successfully captured unencrypted HTTP Basic Auth tokens during the interception window.
- ✦ Immediate Containment Data: generates a boardroom-ready PDF report with precise isolation data — exact rogue MAC and IP address — allowing network engineers to instantly revoke switch port access and quarantine the threat.
Wireshark Manual Analysis vs. PcapAI
Manual (Wireshark) - PCAP
Setting arp.duplicate-address-detected display filters, manually exporting endpoint MAC lists to Excel, and correlating traffic across TCP streams. Process takes 30-60 minutes.
PcapAI - PCAP
Instant extraction of the ARP state machine, automated threat mapping, and cleartext payload correlation. Process takes under 20 seconds.
How It Works
Upload Your PCAP
Drop any .pcap or .pcapng file — up to several GB. No installation, no account required.
AI Reconstructs the Network
Our engine tracks the full ARP state machine, maps all endpoints, and flags behavioral anomalies across every packet.
Get Actionable Findings
Receive a full report with rogue MAC/IP, MITRE ATT&CK mappings, and isolation steps — ready to act on immediately.
Frequently Asked Questions
How do you detect ARP spoofing in Wireshark?
To manually detect ARP spoofing in Wireshark, apply the display filter arp.duplicate-address-detected or navigate to Analyze > Expert Information to look for ARP warnings. This method often triggers false positives from IP conflicts or misconfigured DHCP servers, requiring you to manually verify the MAC address against the legitimate default gateway — a process that can take 30-60 minutes on large captures.
What is MITRE ATT&CK T1557.002?
MITRE ATT&CK T1557.002 refers to ARP Cache Poisoning, a specific Adversary-in-the-Middle (AitM) technique. An attacker broadcasts spoofed ARP messages on a local network segment to associate their MAC address with another host's IP — typically the default gateway — allowing them to silently intercept and inspect network traffic.
What is the difference between ARP spoofing and ARP poisoning?
ARP spoofing and ARP poisoning refer to the same attack. "Spoofing" describes the technique — sending forged ARP replies with a fake MAC address. "Poisoning" describes the result — the victim's ARP cache now contains a corrupted mapping. Both terms are used interchangeably in security tooling and MITRE ATT&CK documentation.
Can ARP spoofing be detected on encrypted networks?
Yes. ARP operates at Layer 2, below TLS or any application-layer encryption. Even on networks where all HTTP traffic is encrypted, ARP poisoning is still visible in packet captures because the forged ARP replies appear in plaintext regardless of upper-layer encryption. PcapAI detects the attack at the ARP layer directly, independent of whether the intercepted payload is encrypted.
What tools detect ARP spoofing automatically?
Several tools can help detect ARP spoofing: XArp and arpwatch monitor live network traffic for ARP anomalies, while Wireshark requires manual filter configuration. For post-incident forensics from a PCAP file, PcapAI automates the full analysis — identifying the rogue host, mapping the attack to MITRE ATT&CK, and generating an isolation report in under 60 seconds without any manual filtering.
Related Use Cases
Test it on your own traffic
Got a suspicious PCAP from your own network? Upload it now and see exactly what PcapAI finds — or view pricing for enterprise team access.
AI Analysis Output (Sample)