The Challenge: Proving Controls to an Auditor
SOC2, PCI-DSS, and HIPAA auditors don't accept firewall logs as proof. They want evidence at the packet level — definitive confirmation that encryption-in-transit is enforced, that unauthorized tools aren't running on the internal network, and that sensitive data isn't leaking across unprotected protocols.
Getting that evidence manually means digging through gigabytes of raw PCAP files, writing custom Wireshark filters for each control, and correlating findings back to specific framework requirements — a process that can take days and still leave gaps an auditor will find.
Malicious insiders and compromised endpoints use tools like sqlmap to quietly map internal vulnerabilities. Finding automated injection scans buried in normal business traffic requires complex, time-consuming Wireshark filters.
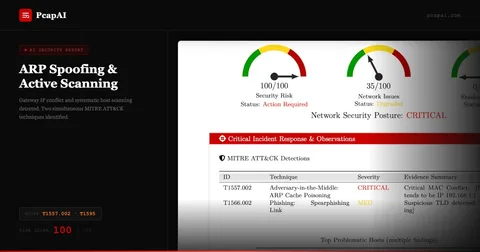
Proving 100% encryption-in-transit for PCI-DSS Requirement 4.2 demands tedious protocol analysis across every session. A single unencrypted login is enough for a critical audit failure.
"We failed our initial SOC2 check because an internal developer was running unauthorized SQL injection scans against our staging environment. Finding the evidence in the PCAPNG files retroactively took our incident response team three days of manual filtering."
— Head of Security, B2B SaaS Company
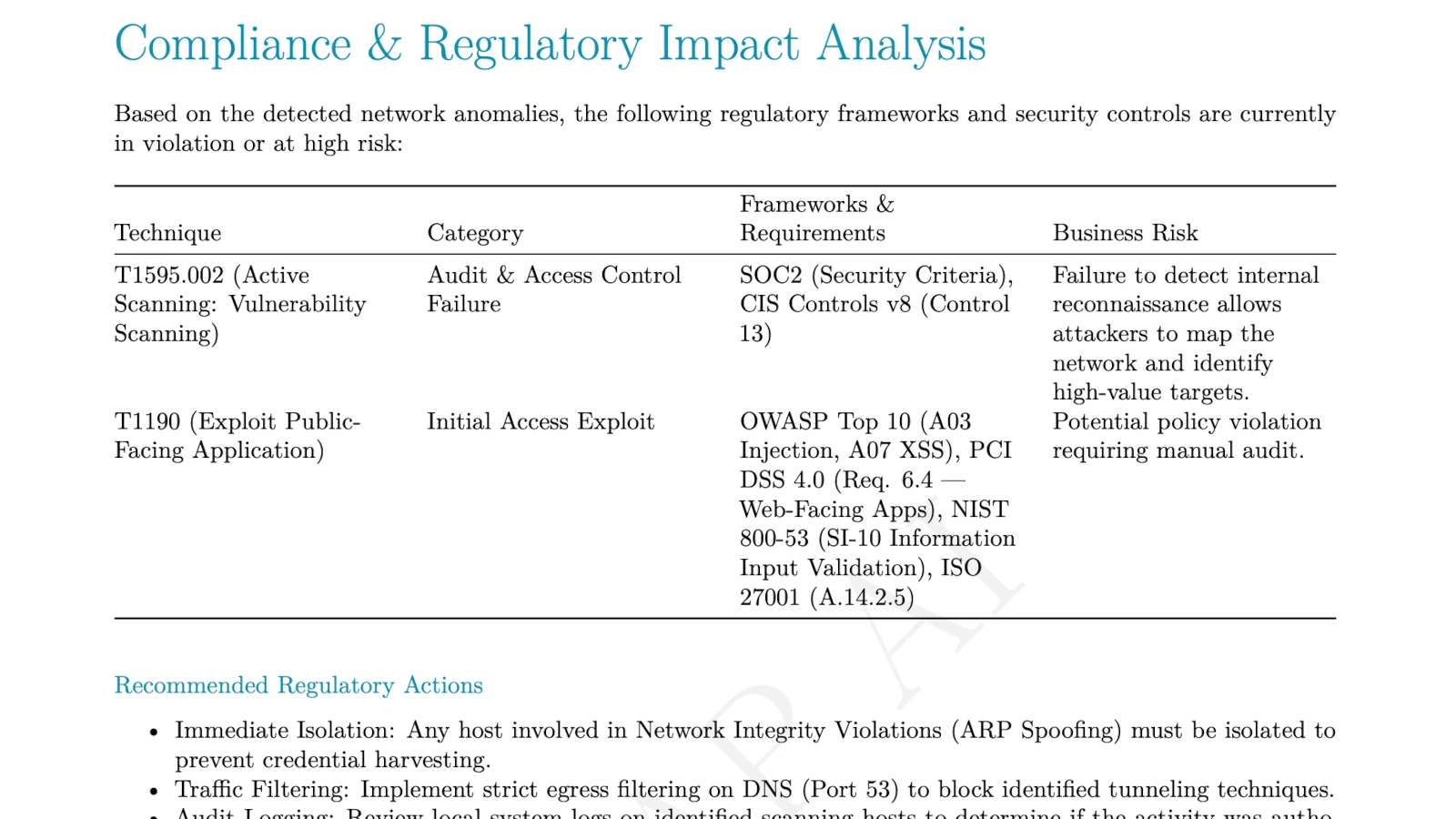
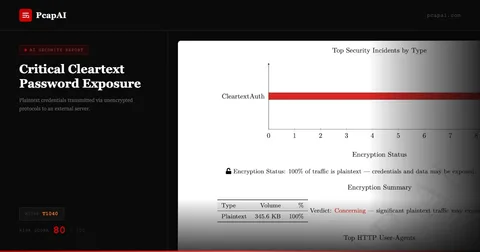
The Solution: Automated Regulatory Mapping
PcapAI acts as an automated forensic auditor for your network traffic. Upload a capture and our deep packet inspection engine instantly identifies active threats, validates encryption status, and maps every finding directly to the specific control requirements your auditor will ask about — in seconds, not days.
-
✦
MITRE T1595.002 (Vulnerability Scanning): automatically flags suspicious HTTP User-Agent strings (e.g.,
sqlmap/1.10.2#stable) and rapid SQL injection payloads originating from internal IPs — with the exact source address and timestamp for your incident report. - ✦ SOC2 & PCI-DSS 4.0 Control Mapping: correlates detected anomalies to specific compliance requirements — linking unauthorized scanner activity to SOC2 Security Criteria and PCI-DSS Requirement 6.4, with the control reference included in the report.
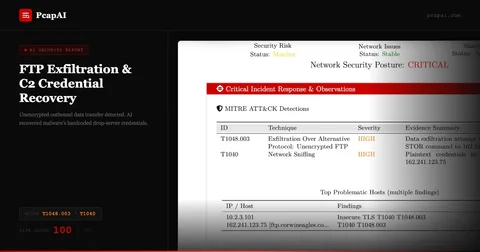
- ✦ Encryption-in-Transit Validation (MITRE T1040): instantly calculates what percentage of sensitive traffic is plaintext versus encrypted, identifying every unencrypted HTTP Basic Auth or FTP session before an auditor does.
- ✦ Auditor-Ready PDF Report: generates a TLP:CLEAR forensic report with an executive risk score, control-mapped findings, and redacted credentials — ready to hand to an auditor or a CISO without further editing.
Wireshark Manual Analysis vs. PcapAI
Manual (Wireshark) — 2.5GB PCAP
Filtering by http.user_agent contains "sqlmap", manually identifying SQLi payloads across TCP streams, cross-referencing findings with compliance frameworks. Process takes 1–3 hours.
PcapAI — 2.5GB PCAP
Automated scanner detection, cleartext protocol auditing, and direct mapping to SOC2, PCI-DSS, and NIST 800-53 controls. Process takes under 20 seconds.
How It Works
Upload Your PCAP
Drop any .pcap or .pcapng from a firewall, core switch, or network tap. No installation, no account required.
AI Audits Every Control
Our engine checks encryption status, detects unauthorized scanners, flags policy violations, and maps each finding to PCI-DSS, SOC2, and NIST 800-53 requirements automatically.
Hand the Report to Your Auditor
Get a TLP:CLEAR PDF with control-mapped findings, a risk score, and redacted credentials — ready to submit without further editing.
Frequently Asked Questions
How do you detect sqlmap in a packet capture?
In Wireshark, filter for http.user_agent contains "sqlmap" to find the tool's distinctive User-Agent string, then manually inspect each stream for rapid repetitive SQL injection payloads from a single source IP. This works but is slow and misses variants that spoof their User-Agent. PcapAI detects sqlmap behaviorally — flagging the injection pattern itself regardless of User-Agent — and maps the finding to MITRE T1595.002 and the relevant PCI-DSS control automatically.
Can PCAP analysis help with SOC2 or PCI-DSS compliance?
Yes — and for many controls, it's the only way to get ground-truth evidence. Firewall logs tell you what was allowed or blocked; packet captures tell you what actually happened on the wire. Deep packet inspection can prove encryption-in-transit (PCI-DSS Requirement 4.2), detect unauthorized internal scanning (SOC2 CC6.6), and surface lateral movement attempts — all with timestamped, forensic-grade evidence that satisfies auditors who don't accept log-based assertions.
Which PCI-DSS 4.0 requirements can PCAP analysis satisfy?
PCAP analysis is most directly applicable to PCI-DSS 4.0 Requirement 4 (protect cardholder data in transit with strong cryptography), Requirement 6.4 (protect web-facing applications from attacks), and Requirement 11.5 (detect and respond to network intrusions). PcapAI maps findings to these specific requirements automatically, generating the control-referenced evidence your QSA needs without manual cross-referencing.
What is the difference between SOC2 and PCI-DSS network requirements?
PCI-DSS is prescriptive — it specifies exact technical controls like TLS version minimums, firewall rule requirements, and prohibited protocols. SOC2 is principles-based — auditors assess whether your controls are suitably designed and operating effectively, with more room for interpretation. In practice, PCAP evidence satisfies both: it demonstrates that your encryption controls work (PCI-DSS) and that your monitoring detects anomalous activity (SOC2 CC7.2).
How often should compliance teams capture and analyze network traffic?
Most frameworks don't mandate a specific frequency for PCAP analysis, but best practice is to capture and analyze traffic at least quarterly, after any significant network change, and immediately following any security incident. PcapAI supports on-demand analysis — upload a capture whenever you need evidence, without scheduling or infrastructure overhead. For continuous monitoring, our API allows automated PCAP uploads from CI pipelines or SIEM integrations.
Related Use Cases
Your next audit is closer than you think.
Upload a PCAP from your network now and see exactly what a QSA or SOC2 auditor would find — before they do.
AI Analysis Output (Sample)