What Is PcapAI?
AI-powered PCAP analysis and deep packet inspection — no software to install, no manual filter-building. Upload a capture file and get a full security report in under two minutes.
PcapAI is a web-based platform that uses artificial intelligence to analyze PCAP and PCAPNG network capture files automatically. Where traditional tools like Wireshark require hours of manual inspection, filter-building, and cross-referencing, PcapAI transforms the same raw packet data into a structured, actionable security report in under two minutes — with no software to install, no command-line expertise required, and no sensitive data retained beyond 24 hours.
The platform was built for the reality of modern security operations: networks are faster, captures are larger, and SOC teams are smaller than ever. Manual packet analysis does not scale. PcapAI fills that gap by combining a high-performance Rust-based packet engine with machine learning models trained on real-world attack patterns, protocol anomalies, and network forensics scenarios.
How PcapAI Works
The analysis pipeline runs in three stages after a file is uploaded.
Parsing & Metadata Extraction
A custom Rust engine deconstructs the binary capture file and extracts structured metadata: flow statistics, protocol hierarchy from Ethernet to application layer, DNS queries, HTTP headers, SSL/TLS certificate details, and raw credential patterns in unencrypted traffic. Typically completes in seconds, even for captures in the tens of megabytes.
AI-Powered Pattern Recognition
Unlike signature-based IDS that only match known patterns, PcapAI's machine learning models analyze context — correlating packet sequences, timing intervals, flow volumes, and protocol deviations to surface anomalies that static rules would miss. Findings are mapped directly to MITRE ATT&CK techniques.
Report Generation
Findings are compiled into a professionally formatted PDF with two audiences in mind: detailed flow tables, packet-level evidence, and technical indicators for analysts; and an executive summary with risk scores and remediation priorities for CISOs and compliance teams.
Who Uses PcapAI
Three primary audiences, one shared problem: too much raw packet data, not enough time to analyze it manually.
SecOps & SOC Analysts
Use PcapAI during incident response to quickly triage captures and identify active C2 communication, credential theft, lateral movement, or data exfiltration — before committing hours to manual Wireshark analysis.
DevOps & NetOps Engineers
Use it for network performance troubleshooting. PcapAI automatically surfaces TCP retransmission storms, ARP conflicts, DNS congestion, and Zero Window events that degrade application performance, correlated with specific hosts and time windows.
Security Consultants & Pentesters
Use PcapAI to accelerate report generation for clients. Rather than manually extracting findings and writing summaries from scratch, upload the PCAP and receive a structured PDF ready to incorporate into a final deliverable.
Core Capabilities
Deep Packet Inspection
Full-stack deep packet inspection across every layer — from Ethernet frames and IP headers down to application-layer payloads. Decodes TCP, UDP, DNS, HTTP, HTTPS, FTP, SMB, SMTP, Kerberos, and more. The result is a complete map of every conversation in the capture: who talked to whom, on which protocol, for how long, and how much data was exchanged.
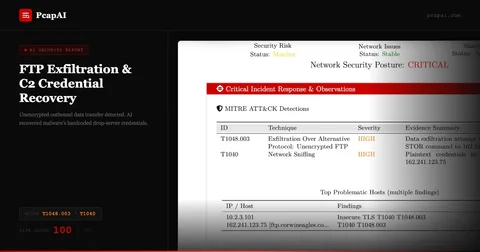
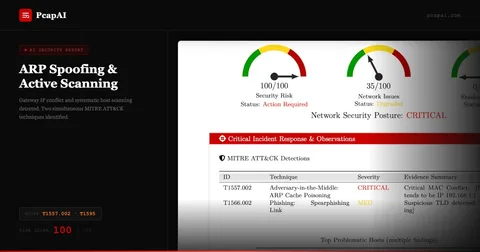
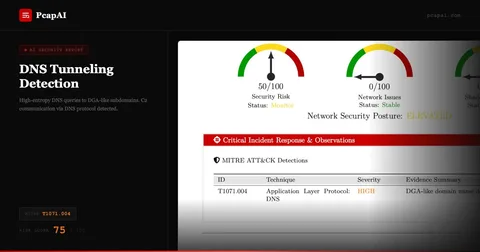
MITRE ATT&CK Threat Detection
Every security finding is mapped to the MITRE ATT&CK framework, giving SOC analysts a standardized taxonomy for communication, escalation, and documentation. The engine covers 60+ techniques — a sample of the most common detections:
- T1071.004 DNS tunneling & C2 over DNS
- T1071.001 C2 beaconing over HTTP/HTTPS
- T1557.002 ARP Cache Poisoning (MITM)
- T1595 Active scanning & reconnaissance
- T1048.003 FTP-based data exfiltration
- T1040 Network sniffing & credential interception
- T1558 Kerberos ticket extraction
These are a sample of the most common detections. The full detection engine covers 40+ MITRE ATT&CK techniques across network-based tactics - from initial reconnaissance and lateral movement to exfiltration and C2 communication. See full coverage matrix →
Credential & Forensic Discovery
Scans application-layer traffic for plaintext credentials, NTLM challenge-response hashes, Kerberos tickets, and session tokens transmitted over unencrypted protocols including HTTP, FTP, SMTP, and SMB. All discovered credentials are immediately masked in the report (displayed as [REDACTED]) — proving the exposure exists without printing the actual secrets, preserving SOC2 and GDPR compliance.
Performance Analytics
Beyond security, PcapAI quantifies network performance degradation automatically. It reports retransmission rates (cases above 60% flagged as critical), calculates per-flow latency, identifies TCP Zero Window events, detects ARP table conflicts causing packet loss, and correlates these metrics to specific hosts and time windows — delivering analysis that would take a network engineer hours to assemble manually.
Automated PDF Security Reports
Every analysis produces a downloadable PDF containing: an executive summary with an overall risk score; a per-finding breakdown with MITRE ATT&CK technique IDs, severity ratings, and remediation steps; flow statistics and protocol distribution tables; and a timeline of detected events. Reports follow a consistent format suitable for compliance auditors, internal security reviews, or client deliverables.
REST API & SIEM Integration
Advanced subscribers can automate the entire workflow via REST API. Common integration patterns: auto-uploading captures from CI/CD pipelines after network tests; feeding captures from intrusion detection systems for automated triage; and pushing report findings into SIEM platforms like Splunk, Elastic SIEM, or Microsoft Sentinel.
MCP Server — Local AI Forensics
For organizations where uploading captures to a cloud endpoint is not acceptable — regulated industries, air-gapped environments, high-sensitivity investigations — PcapAI offers an open-source MCP Server built in Rust. The Model Context Protocol integration allows AI assistants like Claude Desktop to perform deep packet inspection entirely on the local machine. No packet data leaves the device. This architecture resolves the fundamental tension between AI-powered analysis and data privacy in network forensics.
Learn about the MCP ServerPrivacy & Security Architecture
PcapAI was designed with a security-first posture, appropriate for a tool whose users regularly handle sensitive internal network data.
- All file transfers use TLS 1.3 encryption in transit. Files are encrypted at rest during processing.
- Each analysis runs in an isolated container with no persistence between sessions.
- Both the uploaded capture file and the generated report are automatically and permanently deleted exactly 24 hours after upload.
- PcapAI does not extract, store, or transmit any user-identifiable information from packet captures.
Compliance Use Cases
PcapAI reports are structured to directly support common compliance and audit requirements.
Requirement 1.2 and network segmentation validation. Identifies unauthorized lateral communication paths and ARP-based MITM infrastructure.
Detection of unencrypted ePHI transmission. Any plaintext data flowing over HTTP, FTP, or SMTP is flagged with specific flow details.
DoS protection and network boundary enforcement. TCP storm detection and ARP spoofing findings map directly to SC-5 control evidence.
Active scanning detection (T1595) and reconnaissance activity maps to monitoring and intrusion detection criteria in SOC2 Trust Services Criteria.
Credential and PII exposure in cleartext protocols. Provides the technical evidence trail required for breach notification and impact assessment.
Network monitoring and defense. PcapAI findings can be submitted directly as evidence for Control 13 implementation.
PcapAI vs. Manual Analysis
| PcapAI | Manual (Wireshark + Analyst) | |
|---|---|---|
| Time to first finding | Under 2 minutes | 30 min to several hours |
| MITRE ATT&CK mapping | Automatic | Manual lookup |
| Credential detection | Automated, masked in report | Manual, error-prone |
| PDF report | Included | Hours of documentation work |
| Consistency | Every capture analyzed identically | Varies by analyst and fatigue |
| Scalability | API-driven, unlimited parallelism | Bottlenecked by headcount |
| Local/offline option | MCP Server (open source) | Wireshark (always local) |
PcapAI is not a replacement for expert network forensic analysis in complex investigations. It is a force multiplier — handles the first 80% automatically so analysts can focus on the findings that actually matter.
Frequently Asked Questions
Get Started in Minutes
Upload a PCAP file — no account required for a single analysis. Results delivered as a downloadable PDF within minutes.