The Challenge: Spotting Stealthy Infostealer Tunnels
When an endpoint gets infected by an infostealer like PhantomStealer, the malware immediately establishes a C2 channel — periodic HTTP or HTTPS requests to attacker infrastructure, timed to blend in with normal web browsing. Every 10 seconds. Quietly. Until it's done.
The collateral damage makes it worse: aggressive beaconing saturates local network buffers, triggering DNS congestion, TCP Zero Window events, and retransmission storms that flood your monitoring systems with operational alerts — burying the actual root cause under noise that looks like an infrastructure problem, not a breach.
Finding a 10-second beacon interval among millions of legitimate HTTP requests requires writing complex Wireshark filters like http.request.method == "GET" and manually calculating packet time deltas — stream by stream.
DNS gateway congestion causing 265ms latency and repeated TCP Zero Window events generates a flood of operational alerts — making the actual C2 beacon invisible behind what looks like a network performance incident.
"Tracking down a stealthy HTTP beacon in a massive PCAPNG file feels like finding a needle in a stack of needles. By the time I manually filter the TCP streams and map out the exact 10-second request intervals, the adversary has already finished exfiltrating the credentials."
— Threat Hunter, Enterprise SOC
The Solution: AI-Powered C2 Tunnel Detection
PcapAI detects what manual analysis misses: the statistical pattern underneath the noise. Instead of filtering individual packets, our engine analyzes inter-request timing, payload entropy, and protocol behavior across the entire capture — automatically separating a 10-second C2 beacon from millions of legitimate HTTP requests, and correlating it with the secondary network degradation it causes.
-
✦
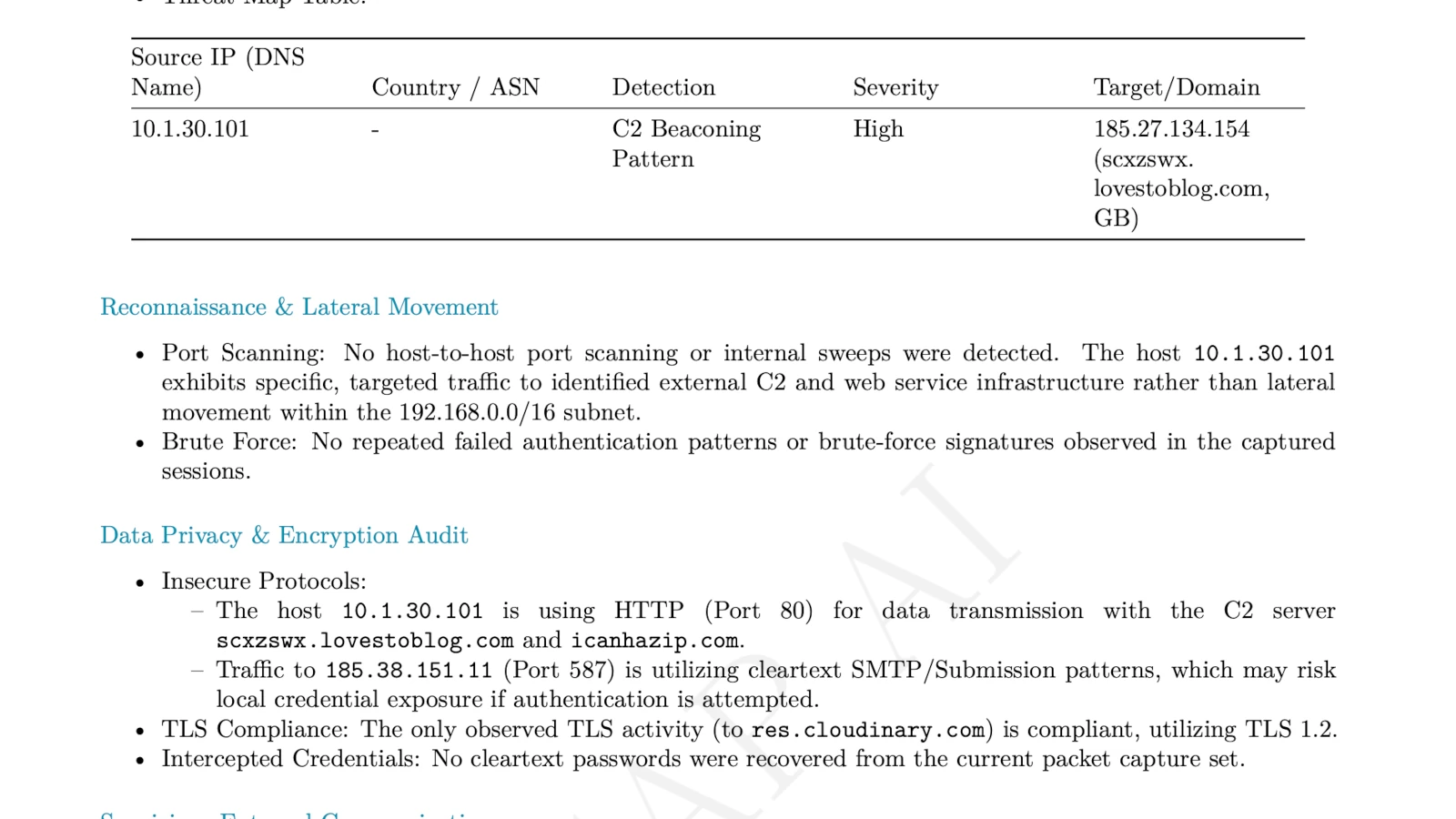
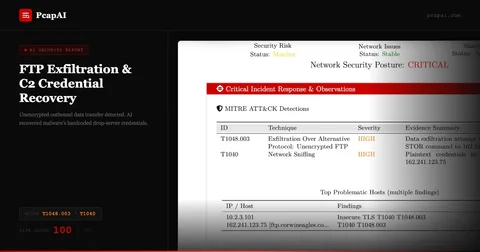
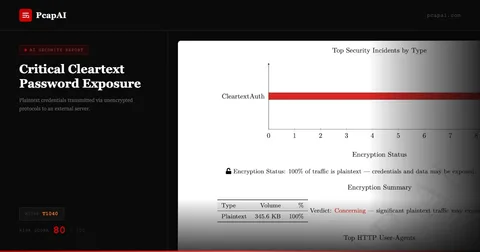
MITRE T1071.001 (Application Layer Protocol: Web Protocols): instantly detects periodic beaconing every 10 seconds from the victim host (e.g.,
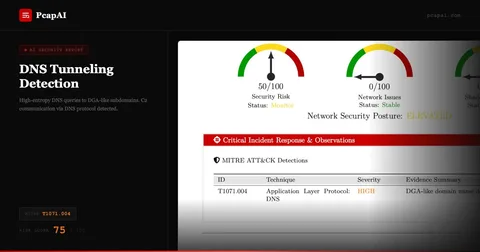
10.0.2.15) to attacker infrastructure at185.27.134.154— with exact timestamps and interval analysis. - ✦ MITRE T1048.003 (Exfiltration Over Alternative Protocol): flags unauthorized outbound SMTP relay attempts on port 587, identifying secondary exfiltration channels that bypass standard web proxies and go unnoticed by HTTP-focused monitoring.
-
✦
Suspicious Payload Extraction: automatically identifies anomalous HTTP GET requests retrieving staged credential files (e.g.,
/arquivo_20260129190545.txt) without manual stream reassembly or URI inspection. - ✦ Root Cause Correlation: links the C2 beaconing directly to collateral network degradation — TCP retransmission rates up to 39.47%, DNS congestion at 265ms latency — proving the performance incident and the security incident are the same event.
Wireshark Manual Analysis vs. PcapAI
Manual (Wireshark) — 1.2GB PCAP
Applying http and tcp.analysis.retransmission filters, exporting packet objects, and manually calculating time deltas across thousands of HTTP streams. Process takes 1–3 hours.
PcapAI — 1.2GB PCAP
Automated beacon interval detection, HTTP payload extraction, SMTP flagging, and MITRE T1071.001 mapping with full root cause correlation. Process takes under 20 seconds.
How It Works
Upload Your PCAP
Drop any .pcap or .pcapng — from an EDR-triggered capture, endpoint isolation, or network tap. No account required.
AI Detects the Beacon Pattern
Our engine analyzes inter-request timing, payload entropy, and protocol behavior across the full capture — identifying periodic C2 intervals that manual filtering misses entirely.
Get the Full Incident Picture
Receive C2 IPs, beacon intervals, exfiltration channels, and correlated network degradation — all mapped to MITRE ATT&CK and ready for escalation or containment.
Frequently Asked Questions
How do you detect C2 beaconing in Wireshark?
In Wireshark, apply http.request.method == "GET" to isolate outbound HTTP requests, then use Statistics > Flow Graph to visualize timing patterns. Detecting a regular interval — like a 10-second beacon — requires manually calculating time deltas between hundreds of requests from the same source IP. PcapAI automates this statistical analysis across the full capture, detecting periodic beacon intervals and flagging the C2 host in seconds.
What is MITRE ATT&CK T1071.001 and why is it dangerous?
MITRE T1071.001 describes adversaries using standard web protocols — HTTP and HTTPS — for C2 communication. It's particularly hard to detect because malicious beacon traffic is structurally identical to legitimate web browsing: same ports, same protocols, same User-Agent strings. Only the timing pattern and destination IPs reveal the difference — and spotting those manually in a large capture is extremely time-consuming.
Why does infostealer malware cause high TCP retransmissions?
Aggressive C2 beaconing and credential exfiltration saturate the infected host's network buffers, triggering TCP Zero Window conditions and forcing the network stack into retransmission storms — often reaching rates above 30–40%. These secondary performance anomalies are frequently the first visible symptom, misdiagnosed as a network infrastructure problem until someone looks at the actual packet data and finds the beacon underneath.
What is PhantomStealer and how does it exfiltrate data?
PhantomStealer is an infostealer malware family that harvests browser credentials, session cookies, and saved passwords from compromised endpoints. It uses two exfiltration channels: periodic HTTP beaconing (MITRE T1071.001) to a hardcoded C2 server for command receipt and status updates, and SMTP relay on port 587 (MITRE T1048.003) for bulk credential delivery. The dual-channel approach means blocking one exfiltration path does not stop the other.
What tools detect C2 beaconing automatically?
Live detection tools like Zeek with the Beacon Detection package and Suricata with ET Pro rules can alert on C2 beaconing in real time, but require significant infrastructure and tuning. For post-incident forensics from a PCAP file, PcapAI automates the full analysis — beacon interval detection, payload extraction, SMTP flagging, root cause correlation, and MITRE ATT&CK mapping — in under 60 seconds with no installation required.
Related Use Cases
Try it with the original PCAP
The traffic analyzed in this case study was sourced from
malware-traffic-analysis.net.
Download the exact .pcap and run it through PcapAI yourself — or upload your own capture to see what's beaconing on your network. Or view pricing for enterprise API access.
AI Analysis Output (Sample)